Every wondered how Anonymous and other hacktivists manage to steal the data or crash the servers of websites belonging to some of the world biggest organisations? Thanks to freely available online tools, hacking is no long the preserve of geeks, so we've decided to show you how easy it is to do, in just four easy steps.
Step 1: Identify your target
While Anonymous and other online hacktivists may choose their targets in order to protest against perceived wrong-doing, for a beginner wanting to get the taste of success with their first hack, the best thing to do is to identify a any website which has a vulnerability.
Recently a hacker posted a list of 5,000 websites online which were vulnerable to attack. How did he/she identify these websites? Well, the key to creating a list of websites which are likely to be more open to attack, is to carry out a search for what is called a Google Dork.
Google Dorking, also known as Google Hacking, enables you find sensitive data or evidence of vulnerabilities by querying a search engine like Google or Bing. It basically allows you to enter a search term into Google and find websites which may have these vulnerabilities somewhere on the site.
Don't worry about needing technical expertise to know what to look for. Kind-hearted hackers have produced lists of these Google Dorks, neatly categorised into the type of vulnerability you are looking for. Looking for files containing passwords? There's got a Dork for that. Login credentials? There's a Dork for that.
For example, if you are looking for files stored on websites containing passwords, then a sample search query we found openly listed on one indexing site was: intitle:"Index of" master.passwd. This returns the results shown in the screengrab above.
So now you have a list of potential victims. Next you need to narrow this down even further.
Step 2: Check for vulnerabilities
Having a huge number of sites which may or may not be vulnerable is not much use unless you can pinpoint one which is actually open to attack. This is when a programme called a vulnerability scanner comes into its own and the most popular is called Acunetix.
Acunetix, developed by a UK-based company, was designed, and is still used, as a tool for web developers to test sites they are building. However the hacking community has commandeered the tool and uses it to identify existing vulnerable sites.
You can download a trial version of the software for free from the official Acunetix website or if you venture into the murky depths of a hacker forum and search for Acunetix, you can find cracked versions of the full application freely available.
Acunetix, as you can see from the screen shots above, is a simple, straight-forward Windows application and all you need to do is enter the URL of the site you want to target, and press Process. Acunetix will scan the entire website, including all pages associated with it, and return a list of vulnerabilities it finds. If you find the type you are looking for, you will need to move onto Step 3, as Acunetix does not perform any website penetration.
Step 3: Attack the website
Attacking a website is done by two main methods. The first is by carrying out a Distributed Denial of Service (DDoS) attack which overwhelms a website's servers and forces it to shut down. We will deal with this type of attack later, but first we will look at how you can hack into an account and steal some information contained within databases on the site.
This type of attack is known as a SQL (pronounced sequel) Injection. A SQL Injection attack aims to capture information stored in a database on the particular website by introducing some SQL code. SQL is a programming language designed for managing data in a database.
But fear not, you won't need to understand a single line of SQL to carry out this attack. Thankfully another freely-available and easy-to-use application, originally developed in Iran, can be downloaded from the web saving you the trouble of dealing with any complex code.
The program is called Havij, the Farsi word for carrot, which is also a slang word for penis and so, unsurprisingly, this is the piece of software required to penetrate a website.
Again there are free and paid-for versions of Havij available with the paid-for version having more powerful capabilities. Again the world of hacker forums is your friend here and cracked versions of the full Havij application are available if you look for them.
The Havij interface is once again like any other Windows program and all a virgin hacker needs to do is simply copy-and-paste the address of their target website and press a button.
Havij allows you to perform a number of different types of operation including one called a Get, which unsurprisingly gets all the information stored on databases on that particular site which can be usernames, passwords, addresses, email addresses, phone numbers and bank details.
And that's it, within minutes you can search for, download and use a couple of automated tools which will allow you to access websites which are vulnerable to this type of attack. While most high profile companies' websites will be protected from this type of attack, the fact that Sony's website and the personal information of its customers was stolen in a manner similar to this, shows just how vulnerable the web is.
Step 4: If all else fails, DDoS
Hacktivist collective Anonymous changed their tactics in the last 12 months moving away from DDoS as their primary tool for attacking websites, preferring if possible to use SQL Injection instead. However, when this is not possible, they will revert to DDoS attacks, and you can to, with the help of another freely available tool.
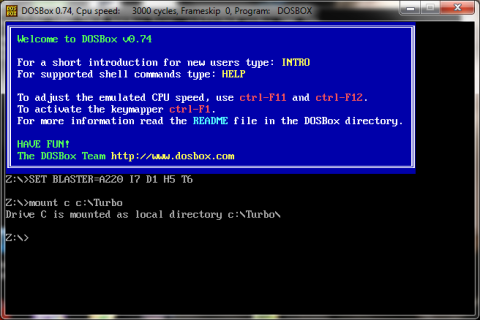
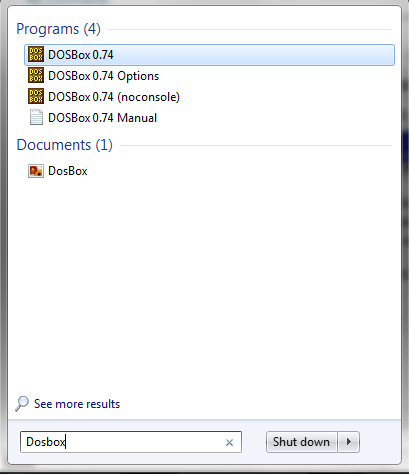
And it turns out that DDoSing a website is no more difficult than carrying out a SQL Injection. The programme used is called Low-Orbit Ion Canon (LOIC) which was developed for web designers to stress test websites, but has been high-jacked by hackers in order to attack websites.
Available as a free download from Source Forge, LOIC employs a very user-friendly interface and all potential hackers need to is type in the URL of the site they want to crash and LOIC will do the rest. What the application will do is send up to 200 requests per second to the site in question.
While most bigger sites might be able to deal with this request without crashing, most websites out there will not, especially if you get together with some other hacking virgins and combine your efforts.
So easy is it to use this technology that you can even control it from your BlackBerry, meaning you can be enjoying a pint in the pub with your friends while carrying out a DDoS attack on a website of your choice.
If our tutorial has not provided you with enough information, there are dozens of other tutorials on various hacker forums around the web and even video tutorials on YouTube which you can watch.